I now have all these VM’s and physical devices; each usually having their own dashboard or other way of monitoring the resources being used. But it is a pain to look in numerous locations to see how much RAM is being used or that my storage drives are full. I could have kept relying on the Xen Orchestra monitoring features to provide 90% of the solution, but that still wouldn’t address the other physical hardware I have like my switch, wireless AP, etc. So I started looking to 3rd party solutions. My “requirements” are it needs to monitor everything I have, support alerting via email, and be open source. Nearly all my hardware (and software via snmp packages) supports SNMP and Syslog, so getting information out shouldn’t be a problem. Syslog is going to ELSA in my Security Onion vm. This post will focus on SNMP.
just my own personal notes that i don't want to forget
Tag: networking
“Security Onion is a Linux distro for intrusion detection, network security monitoring, and log management. It’s based on Ubuntu and contains Snort, Suricata, Bro, OSSEC, Sguil, Squert, ELSA, Xplico, NetworkMiner, and many other security tools. The easy-to-use Setup wizard allows you to build an army of distributed sensors for your enterprise in minutes!”
I virtualized this under my Xenserver all-in-one host. This host has the resources to host a vm like this. It also contains my virtual pfSense firewall performing inter-VLAN routing and numerous virtual machines, so the Open vSwitch bridge is seeing nearly all the packets bouncing around my home network.
One of my interests, as well as my day job, is cyber security. I have dabbled with running an IDS at home for 10+ years now, but as my hardware aged or died, I just didn’t have the tech at home to do it anymore. With the arrival of my new server, time to virtualize an IDS.
In the physical world, this is “easy”. In the old days, I would plug my 10Mbps hub inline between my cable modem and router/firewall. Off the hub I would connect my monitoring server running Snort. Well things have come a LONG way since then. Now with 100Mbps WAN connections becoming the norm, and gigabit networks in the LAN, a hub isn’t going to cut it. On a managed switch I just configure a port mirror (RSPAN) source and destination. Plug monitoring server into the destination and watch the packets!
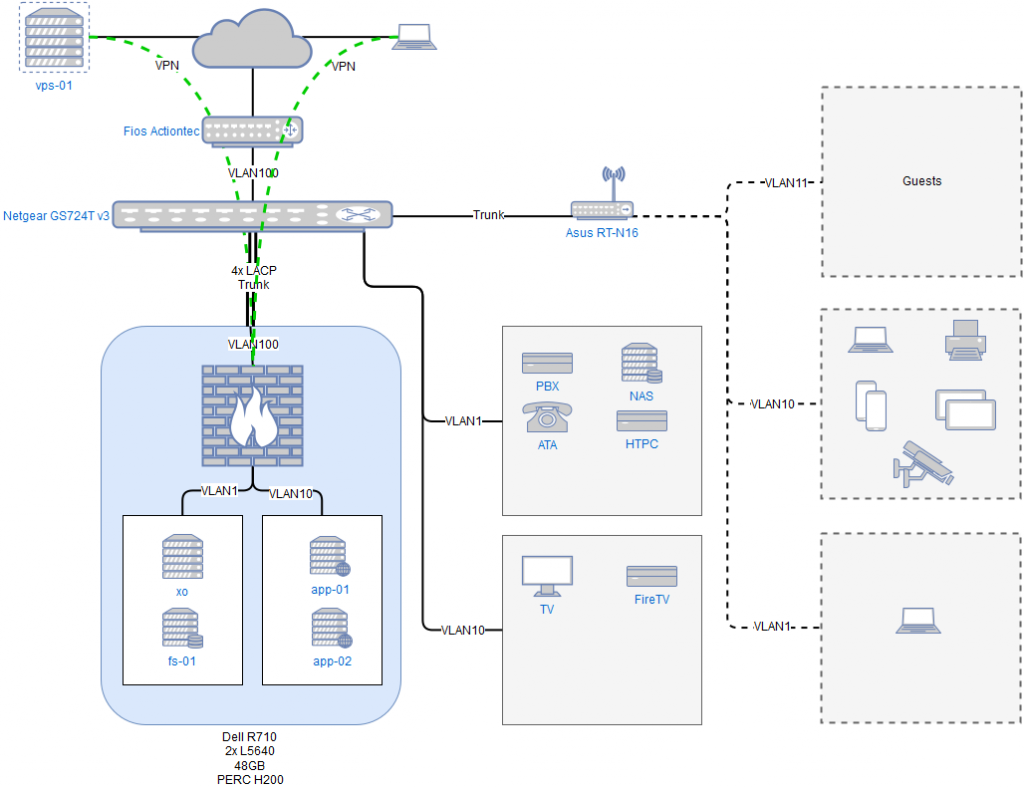
Finally got around to diagramming my network out. Used the online draw.io site to mock it up quickly. It’s a start.
As I stated earlier, I desired different wifi networks depending on how much I trust the device and/or user. More and more things showing up in my house support wifi…that whole Internet-of-things (IoT). The real threat of cryptoware or other malware being brought in by my wife, kids, or guests sent me down this path. And I think it is just cool to do.
I’ve had an Asus RT-N16 802.11n wifi router for years, mostly unused. It is flashed with TomatoUSB firmware already, which exposes many neat tricks. Most of them I don’t need, but a VLAN aware firmware is a must for what I want to do. I could go out and by some cool PoE Ubitquity devices, but that costs $$$….I don’t like spending money. So putting the Asus back into production here we go.

Having been “stuck” with the Verizon provided Actiontec router/firewall since I bought the house, I used my newly acquired Xenserver to virtualize my preferred firewall…pfSense.
.png?itok=XFseGWi-)
I’ve been using pfSense on and off for many years now, but mostly back when I had cable internet. Verizon complicates things. My house came pre-provisioned over coax and I have yet to get around to running a Cat5e cable from the ONT to the area in my basement where I keep my network gear. So I still retain the Actiontec upstream and am effectively double NAT-ed. Since I don’t game or torrent, I’m not concerned right now.
As I planned my new home network to include different SSID’s, I needed to implement more than one VLAN and inter-VLAN routing to segregate the traffic. My previous method of uplinking multiple 10/100 and 10/100/1000 consumer 5-port switches to handle all the connections I needed was just not going to work any longer. So I started looking for a Layer 2 managed switch to pair with pfSense (will handle the actual routing and firewalling). I initially wanted an HP 1810 24-port, but all were a big more expensive than I wanted to pay. After looking around on and off, I found a Netgear GS724T v3 on Ebay with all manuals, rack ears, and power cable at a price I couldn’t refuse…..score. I realize this is only a “smart” switch and not a fully managed CLI model, but that is good enough for my needs at home.

© 2024 James Timberlake
Theme by Anders Noren — Up ↑
Recent Comments